Hoorah for Security Researchers!
(this blog post is looonggg over due - Sorry!)A while back, I was fortunate enough to stumble across a slide deck by Hyperchem Ma illustrating research into the security concerns of barcodes You can see the presentation slides for yourself here.
This interesting concept got me thinking about what a real attack vector barcodes can be in modern times. In the slides, there is a proof-of-concept scenario that shows how a malicious payload embed into a group of barcodes (automated with a modified Kindle -- genius might I add), can be used to pop a shell on an airplane ticket kiosk.
With my mind thoroughly blown, I wanted to see this in action for myself. Leveraging the slide-deck above and doing some research into the areas where information was omitted, I finally was able to create a working proof-of-concept that would effectivley open a command prompt shell on Windows 7, 8.1, and 10 provided the computer was focused on the Desktop.
Unfortunately, to begin creating and testing payloads, I needed an effective method of quickly generating barcodes containing hex data to simulate keyboard scancodes and key strokes.
...Scansploit is Born
Other than seek out an existing application to generate barcodes, I decided to make my own in python (my python, of which, has gotten much much better since my previous posts...Flask apps, automation, API integration, and moar ..thank you work :D ).Scansploit takes user supplied data either from a string or file and generates it into a barcode format. Formats supported currently are:
- Code128
- QRCodes
- DataMtrix
- EAN13
Scansploit is opensource and available on my github here.
The Payload
I'll spare the details, but after an Amazon order later, much tinkering, and a ton of trial and error, I was able to develop a payload of barcodes that would open up a command prompt shell from the Desktop on Windows 7, 8.1, or 10 (all tested). The payload is much shorter then I originally expected but provides a proof-of-concept that should outline the serious security implications of barcodes as an attack vector. In this case I ran "ipconfig", but an attacker could just as easily extend this payload to use Powershell to wget (as of Powershell 3 <3) an executable payload such as a reverse remote shell, Remote Administration Tool, or any other malware.
Payload:
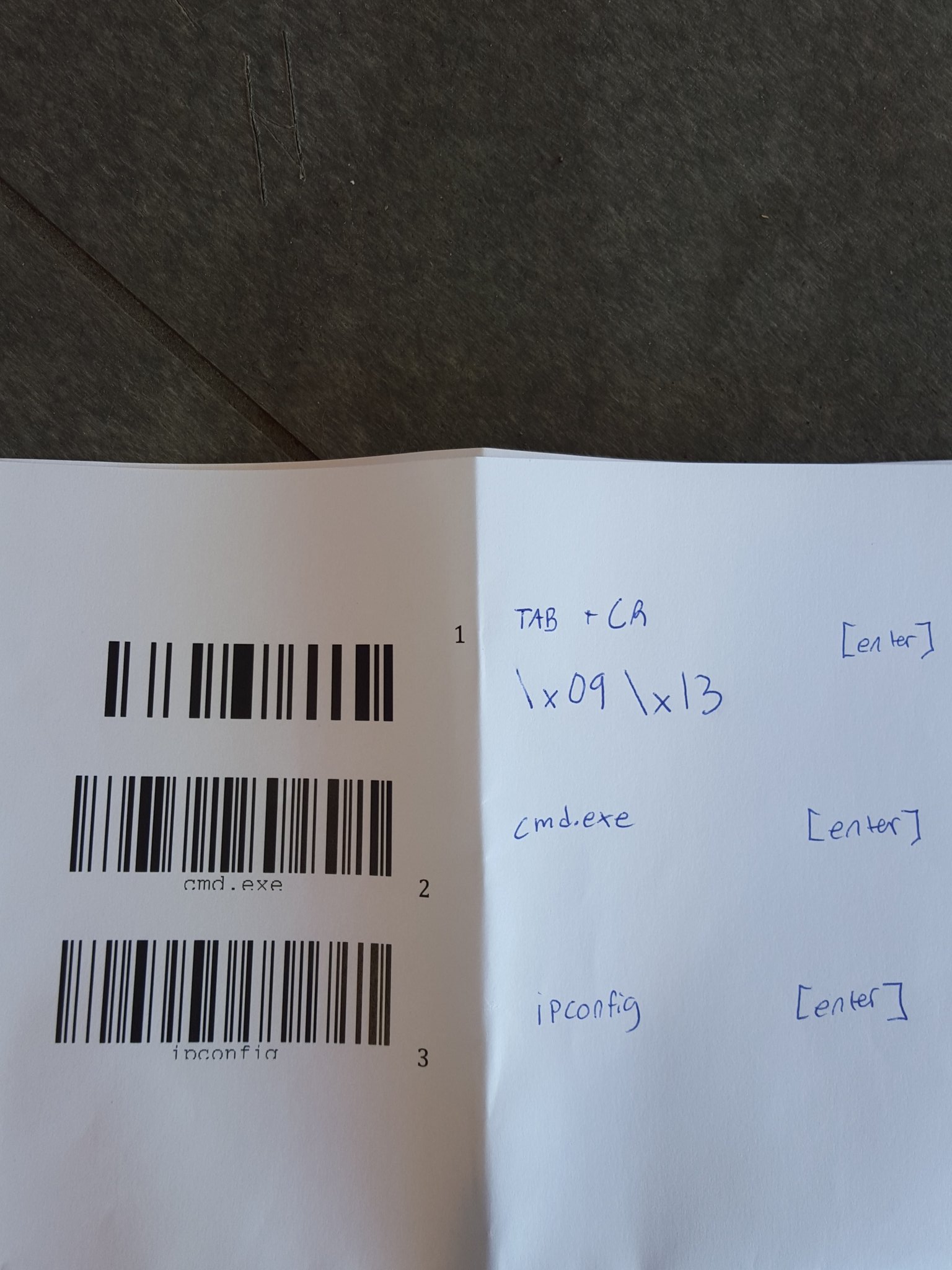
Barcode 1: TAB + Carriage Return (\x09\x13) [enter]
Barcode 2: "cmd.exe" [enter]
Barcode3: "ipconfig" [enter]
 |
| I got some weird looks on campus during the project |
Takeaway
The takeaway from this project is that our world runs on 1's and 0's, and attack vectors are everywhere...even where you would least expect them. Point-of-Sale systems, airplane kiosks, movies rental kiosks, lottery ticket stations, self-checkout stations, and even cell phones all are capable of scanning barcodes. With so many potential targets it should require little explanation as to why the barcode attack vector should be taken seriously.Cheers...and remember to Hack The Planet! (for research and proper disclosure of course!)

No comments:
Post a Comment